NEWS
Consent Phishing: The Emerging Phishing Technique That Can Bypass 2FA

-As Published by TotalCom
Consent phishing is an emerging technique attackers are using to compromise user accounts, even if they have Multi-factor Authentication (MFA or 2FA) enabled. Consent phishing is particularly effective because it doesn’t exhibit many of the indicators that traditionally expose phishing attacks. However, there are sensible controls available.
With more platforms adding support for Multi-factor Authentication (MFA) and users increasingly adopting it to secure their accounts, attackers are adapting and moving to new methods of compromising user accounts. In this post we’ll take a look at consent phishing and how it is being used to bypass MFA and also skirt key attributes of phishing that are taught in traditional user awareness campaigns, such as links to untrusted domains
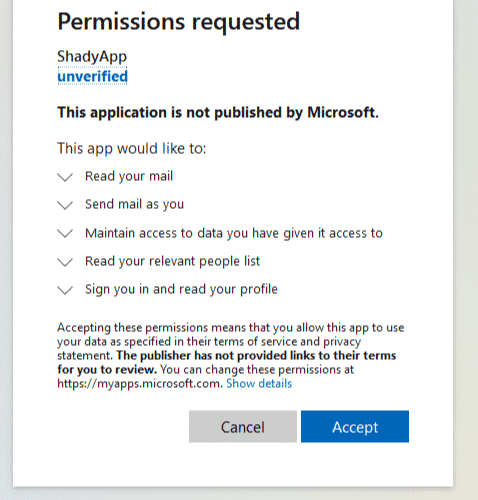
Maybe you’ve been waiting for the latest financials or you suspect this was sent erroneously but you’re curious and want to take a peak. When you click the link you are presented with a prompt that with your Monday brain looks just like the “Yes give me access” prompt you’ve clicked through a thousand times. I mean, it's a microsoftonline.com domain, it's https and there’s a green tick in the corner so everything looks fine.
If you’d looked closely you may have noticed that this was in fact asking you to approve access rather than granting you access. But with your muscle memory in full control you click “Accept” before even glancing at the screen. You wait for the spreadsheet to open but are presented with a generic “File does not exist” error page. Oh well, apparently Karl realised his mistake and deleted the file or revoked your access. Onto the next email.
And just like that you’ve been consent phished. You’ve just granted the attackers permanent access to your account, which they retain even if you change your password or have MFA enabled. Chances are the attacker’s tools will immediately start downloading every piece of data you just granted them access to, which they can then explore at their leisure.
If you’d been paying attention when you clicked “Accept” you might have noticed that you were granting some pretty serious permissions here. These permissions allow the attackers to read and write any files you have access to - they could download all these files and then delete them. The attackers also got permission to send emails as you. They could send emails to your colleagues from you and phish them too, this isn’t impersonation where the email just “looks” like it came from you, the email DID come from you. Lastly the attackers asked for permission to manipulate your Outlook settings, with this they could set up a mail forwarding rule so that they get copies of all your emails forwarded to them directly without even having to log in. And all of this happens until you delete the underlying OAuth app.
Disclaimer
This information is intended to provide general advice only. We recommend you discuss your specific situation with your Accountant.